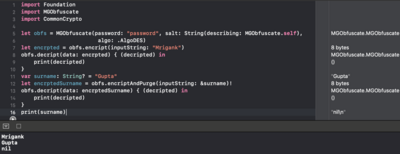
MGObfuscator
October 21, 2019 • Apache 2.0 License
When we are working on apps which have lot of sensitive information (like Banking etc). We should be a lot of careful about strings. There is nice write up why (https://www.raywenderlich.com/2666-i...
SETOCryptomatorCryptor
July 07, 2016 • MIT License
iOS crypto framework to access Cryptomator vaults.
EncryptedChat
November 04, 2015 • MIT License
<b>Features</b><br><br>
Live chat between multiple devices<br>
Group chat functionality<br>
Private chat functionality<br>
Single or Multiple recipients<br><br>
Full realtime actions - lat...
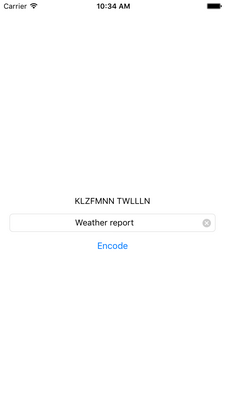
Secure Your App
July 02, 2015 • MIT License
Add an extra layer of security against prying eyes. **IT IS NOT A FAIL-SAFE MEASURE**
Security Sensitive strings can be:
* REST API Credentials
* OAuth Credentials
* Passwords
* URLs not i...
ObjectivePGP - OpenPGP implementation
August 21, 2014 • zlib License
ObjectivePGP is an OpenPGP implementation for iOS and OSX.
MIHCrypto
May 25, 2014 • MIT License
OpenSSL is the most powerful SSL and TLS library available which wraps a full cryptographic library. The library is written in pure C and due to its endless size and not-so-well-designed C interfac...
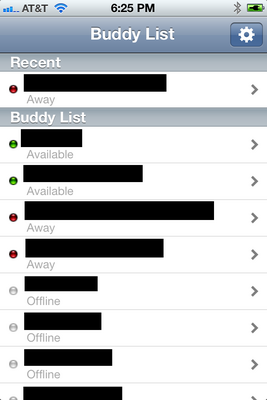
ChatSecure
September 09, 2013 • GPL License
ChatSecure is a simple multiprotocol IM client for iOS that supports encrypted "Off-the-Record" messaging using Cypherpunks' libotr